REPORT: Russian wallets collected US$400m in crypto ransomware in 2021 – and there’s a solid link to Moscow City’s Federation Tower

Moscow City's Federation Tower complex (Getty Images)
It’s suspected that last year Russian cybercriminals were able to net a profit of more than US$400 million in crypto from the use of ransomware-based extortion, according to a new report.
New York-based blockchain analytics firm Chainalysis, which set up a Canberra office in November and has also partnered with the Commonwealth Bank, this week released details from the Russia-focused part of its 2022 Crypto Crime Report.
That section of the upcoming report was shared with Stockhead, and here are the key findings:
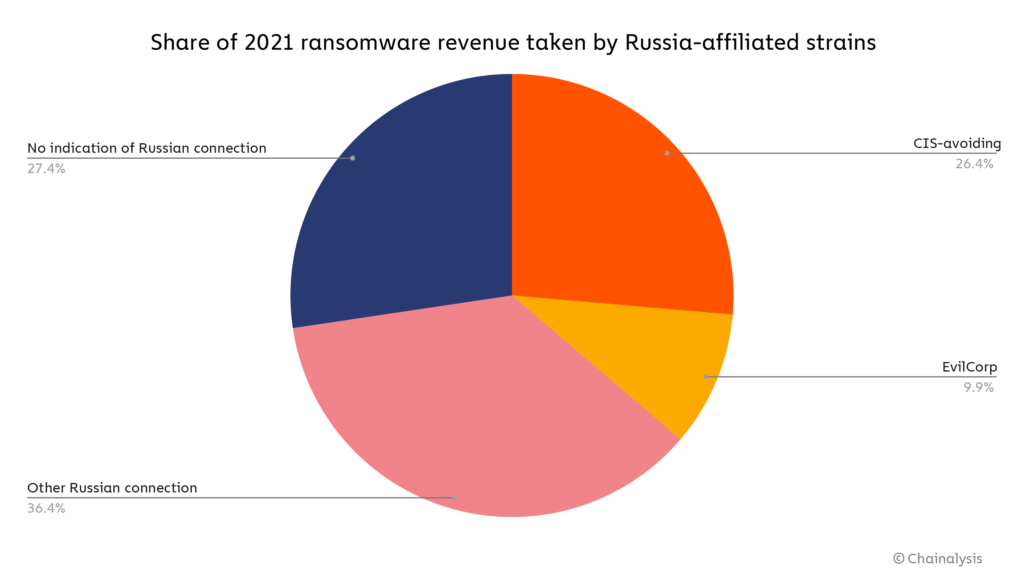
• Approximately 74% – more than US$400 million – of ransomware revenue last year was siphoned into high-risk wallets addresses likely to have been based in Russia.
• After ransomware attacks take place, most of the extorted funds are “laundered through services primarily catering to Russian users”.
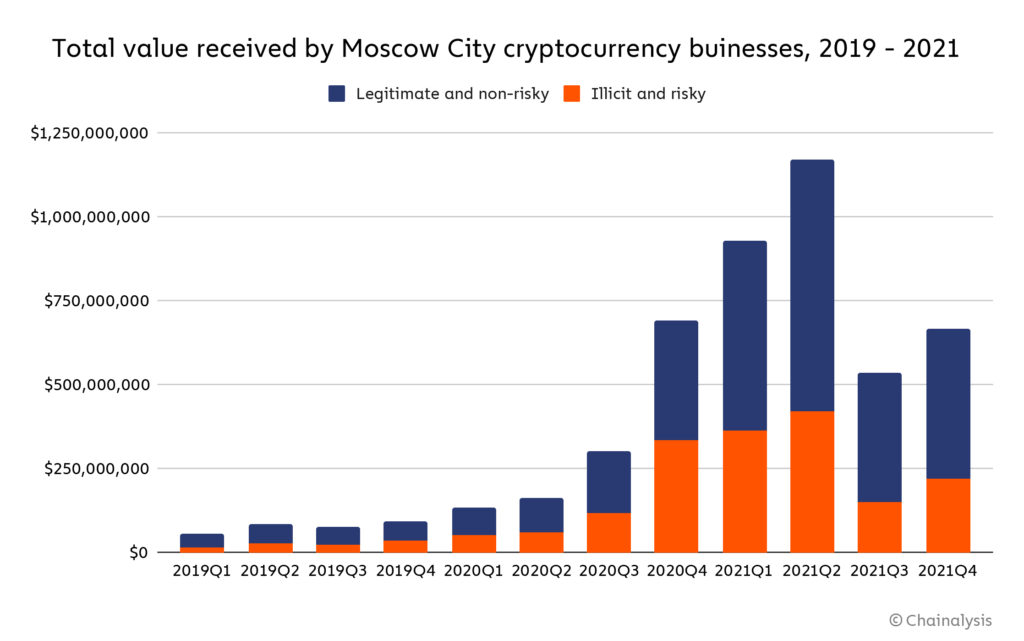
• Chainalysis tracks several dozen crypto businesses operating in Moscow City that appear to facilitate significant amounts of money laundering.
• Over half of those businesses tracked have reportedly operated in the same Moscow City skyscraper: Federation Tower.
The Federation Tower allegation
Federation Tower is a prestigious, two-skyscraper complex in the heart of Moscow City, containing several prominent businesses.
As Chainalysis details, Bloomberg and the New York Times have both recently reported that the complex is home to several crypto businesses that have “facilitated money laundering, accepting funds from addresses involved in various forms of cryptocurrency-based crime — especially scams, darknet markets, and ransomware”.
The report lists some of the businesses with a Moscow City presence that have facilitated the most money laundering, although none of them are well-recognised names in the wider crypto sphere. Also, it should be noted it’s not proven or known whether this, in most cases, has been an unwitting facilitation through lack of security and/or knowledge.
Russian ransomware connection to… EVIL CORP
The report found three common characteristics in last year’s ransomware hacks that determined their suspected Russian affiliation, and those were:
• Ties to “Evil Corp”. Sounding exactly like something from the Austin Powers films, Evil Corp is a Russia-based cybercriminal organisation that has been prolific in ransomware. According to the Chainalysis report, the organisation’s leadership is believed to have ties to the Russian government.
• The avoidance of targeting former Soviet countries. The Commonwealth of Independent States (CIS) is an intergovernmental organisation of Russian-speaking, former Soviet countries, and ransomware has been specifically coded to avoid the extortion happening in those nations.
• Ransomware strains sharing documents in the Russian language. Which is , of course, probably the most glaringly obvious affiliation characteristic.
Russia looks to regulate and legalise crypto
With the cloud of potential Ukraine invasion driving most of the narrative, there’s understandably not a lot of positive sentiment related to Russia right now, but at least this is something for the global crypto economy to grab hold of… for the moment…
As reported by Stockhead last week, Russia’s government and central bank are reportedly in the process of attempting to reach agreement on regulating cryptocurrencies.
The nation’s central bank has recently been trying to red card crypto, calling for all activities related to it, including crypto mining, to be completely banned.
If this agreement is reached, it will be quite the backflip, or back down, from the central bank. Putin and pals apparently see potential in crypto as a legitimate revenue stream, so it would seem likely the government will get its way.
And today, Russia’s Ministry of Economic Development has further proposed regulating and legalising crypto mining in certain areas that can facilitate “sustainable surplus in electricity generation”, according to a Russian media report.
Related Topics
UNLOCK INSIGHTS
Discover the untold stories of emerging ASX stocks.
Daily news and expert analysis, it's free to subscribe.
By proceeding, you confirm you understand that we handle personal information in accordance with our Privacy Policy.